The Largest Platform to Find Cybersecurity Tools
Browse 0 cybersecurity solutions, with 0 security professionals searching monthly
FEATURED
Stay Updated with Mandos Brief
Get strategic cybersecurity insights in your inbox
TRENDING CATEGORIES
POPULAR
WHICH CITIES ARE SHAPING CYBERSECURITY?
2,970+ security vendors mapped by headquarters. See which countries and cities lead the industry — and where the next wave is building.
Discover All 2,970 Companies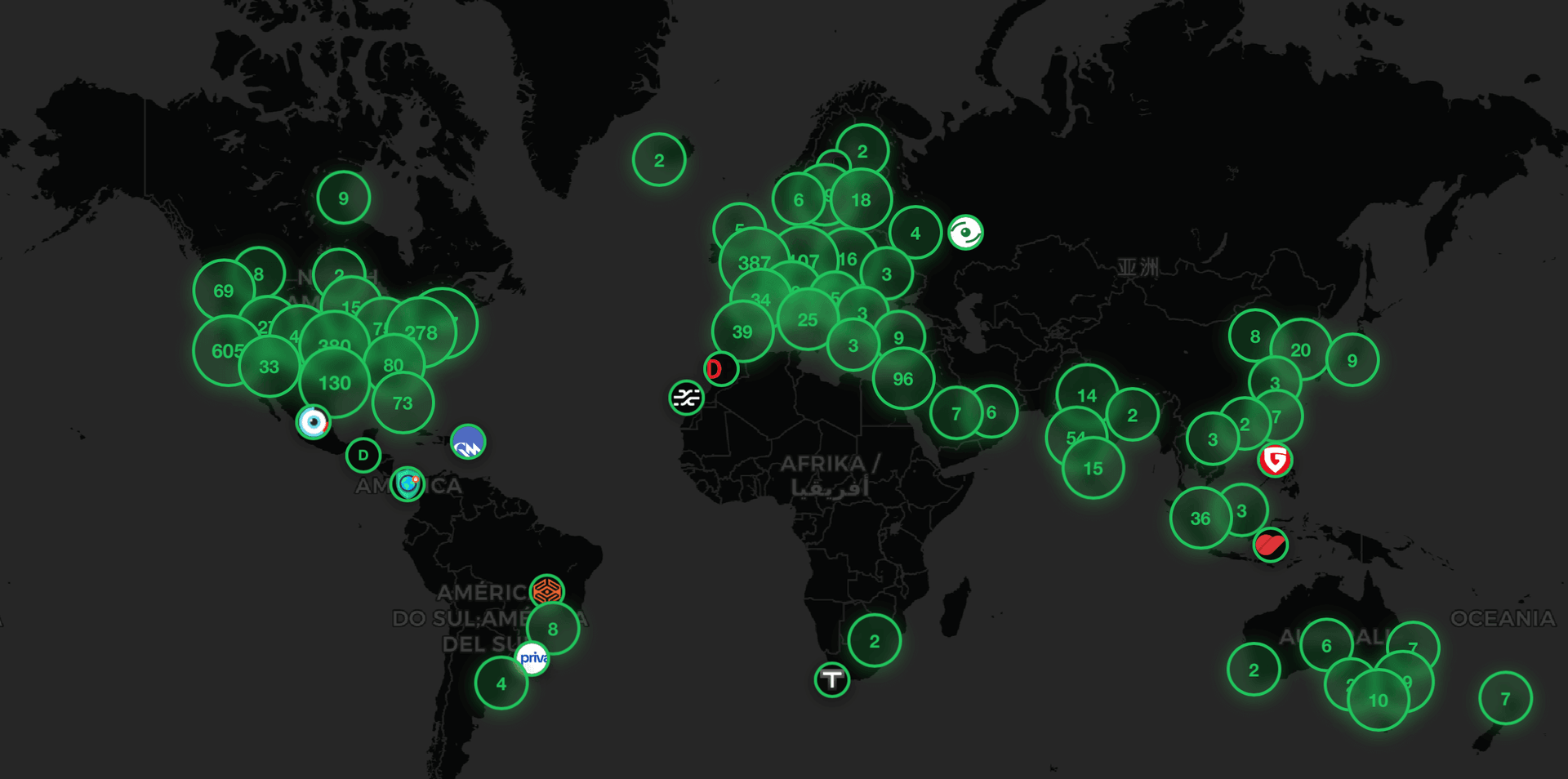
FIND ALTERNATIVES TO
View allBROWSE CATEGORIES
View allSecurity operations tools for SIEM, SOAR, threat hunting, incident response, and security operations center (SOC) management.
Identity and Access Management solutions for identity governance, access control, authentication, privileged access management, and zero trust security.
GRC tools and platforms for managing cybersecurity governance, risk assessment, compliance monitoring, and regulatory reporting.
Application security tools and solutions for securing web applications, mobile apps, and software throughout the development lifecycle.
Vulnerability management tools for security scanning, penetration testing, bug bounty programs, and vulnerability assessment.
Data protection tools and solutions for data encryption, backup, classification, loss prevention, and privacy compliance.
Cloud security tools and solutions for securing cloud infrastructure, containers, serverless applications, and multi-cloud environments.
Network security tools and solutions for firewalls, intrusion detection, network monitoring, and perimeter security.